January 2020
Download
Phishing Attack Hijacks Office 365 Accounts
Be careful about granting permission for apps to access your online accounts. Phishers can gain access by displaying a “Permissions requested” dialog that shows what permissions the third-party is requesting and then asks the user to accept the request.
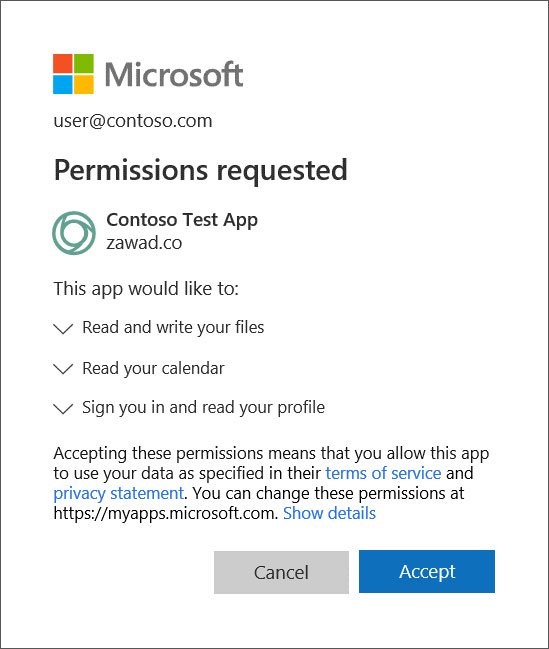
Example App permission request from Microsoft
If the user accepts the app’s request, a security token associated with the user will be sent to the app developer (or hacker), which allows them to access the user’s data and services from their own servers and applications.
The latest Windows Feature Update causes some minor issues with the search function in file explorer.
Ring Devices are a popular hacking target. Make sure yours is secure.
A Data Leak Exposed The Personal Information Of Over 3,000 Ring Users
Hackers keep dumping Ring credentials online ‘for the giggles’
Amazon, Ring Sued Over Weak Camera Security
How to secure your Ring doorbell
The Ring doorbell introduces a potential digital vulnerability to your physical world. If you plan to use it, then make sure you do so securely.
- Safeguard your Wi-Fi with a guest network and use a strong password.
- Do not share your Wi-FI publically – disable SSID broadcast);
- Be sure to attach your device securely so that it can’t easily be stolen;
- Always keep its software up-to-date;
- Do not share Ring videos on social networking apps as it might pose a threat to your security and privacy. In 2009, Ring was criticized for using videos shared on its Neighbors social network to provide tips on suspects;
- Do not keep old footage. Delete it so there would be less information available about you in case of a breach.
Beginning January 15, 2020, Microsoft will be delivering its new Chromium-based Edge browser automatically to Windows 10 users via Windows Update, unless its Edge Blocker Toolkit is applied.
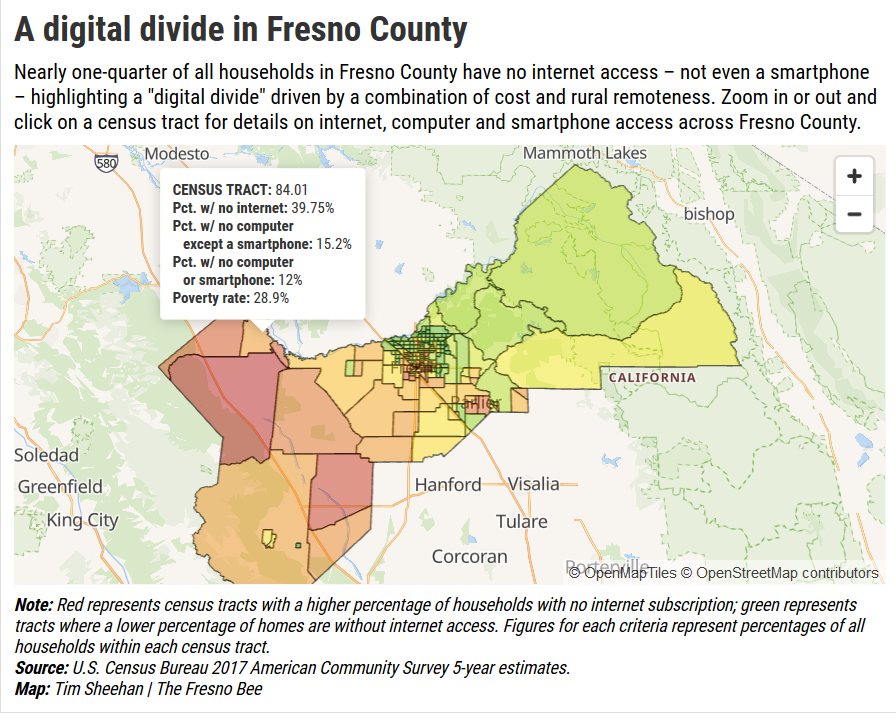
How your activity is tracked and shared by apps, websites, phones, and stores.
Although Facebook doesn’t listen to you through your phone, that’s just because it doesn’t need to. …Trackers assemble data about our clicks, impressions, taps, and movement into sprawling behavioral profiles, which can reveal political affiliation, religious belief, sexual identity and activity, race and ethnicity, education level, income bracket, purchasing habits, and physical and mental health.
Deepfake form submission
“…emerging technology is now capable of developing “highly convincing natural language generation that..makes it nearly impossible to distinguish whether online speech originated from a person or a computer program. More on Deepfake automation. To see how well you can identify deepfake text, take the Deepfake Text Study.
Tech predictions for 2020 from
Inc. Magazine, Forbes (Forrester) NY Times Fast Company
Security
One Day, Three Credit Card Data Breach Notifications
On the same day this week, two restaurants and a convenience store, all with locations across the U.S., disclosed security breach incidents that may have enabled attackers to steal customer payment card data. In all three cases, malware designed to collect magnetic stripe data was discovered on payment processing servers for card transactions.
Around 40% of Security Cameras May Be Unsecure
Our primary research data points to the fact that more than half of the cameras with out-of-date firmware (53.9%) contain known cybersecurity vulnerabilities. By extrapolating this to an average security network, nearly 4 out of every 10 cameras are vulnerable to a cyber-attack,”
Thousands of hacked Disney+ accounts are already for sale on hacking forums
Hackers started hijacking Disney+ user accounts hours after the service launched. Accounts are now being offered for free on hacking forums, or available for sale for prices varying from $3 to $11.
752,000 US birth certificate applications were exposed online
These are the worst hacks, cyberattacks, and data breaches of 2019
LifeLabs Data Breach Exposes Personal Info of 15 Million Customers
Data breach took place in early November, and hackers also gained access to 85,000 laboratory test results.
LifeLabs pays hackers to recover data of 15 million customers
LifeLabs, Canada’s leading provider of laboratory diagnostics and testing services, admitted today to paying hackers to retrieve data stolen during a security breach last month.
Honda exposed roughly 26,000 vehicle owner records
Torian Group
We have increased our hourly rate from $130 to $135 starting January 1, 2020. Travel time will go from $60 to $70 per hour, and server backups will go from $40 to $50 per month. Other prices are unchanged. The last rate change was 2 years ago. As always, let us know if you have any concerns.
By
Tim Torian